Apple.com XSS Gallery
In the past I've reported a lot of security bugs to Google (you find here some stats about the last year) and three months ago I've found in just one night a lot of reflective XSS bugs on different apple.com sites.
If I try to compare both security team, I feel with Google much more comfortable to communicate. Apple is slow in the first response, didn't told me that a bug is fixed and I had to report some bugs twice to get a confirmation that they started working on it.
Compared to other companies Apple has a lot of deprecated (?) legacy applications running. It looks like a mingle-mangle of different programming languages, application servers, domains or hostnames and independently running services - with a lot of bugs.
Did you know, that Apple has a credit page who have reported potential security issues? They call it Apple Webserver Notifications.
Update: Here a explanation from OWASP what XSS is.
Cross-Site Scripting attacks are a type of injection problem, in which malicious scripts are injected into the otherwise benign and trusted web sites. Cross-site scripting (XSS) attacks occur when an attacker uses a web application to send malicious code, generally in the form of a browser side script, to a different end user. Flaws that allow these attacks to succeed are quite widespread and occur anywhere a web application uses input from a user in the output it generates without validating or encoding it.
So, here we go with the XSS Gallery:
discussions.apple.com

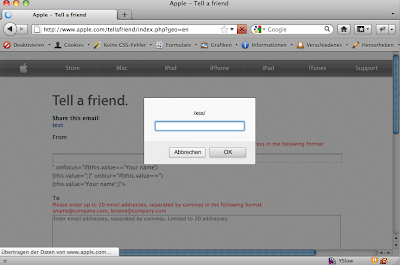
www.apple.com
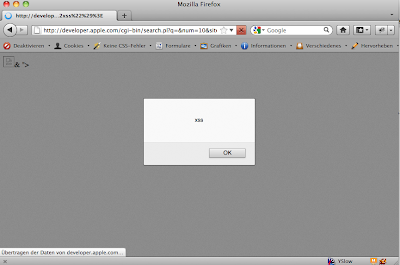
developer.apple.com
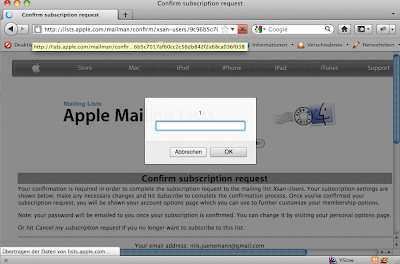
lists.apple.com
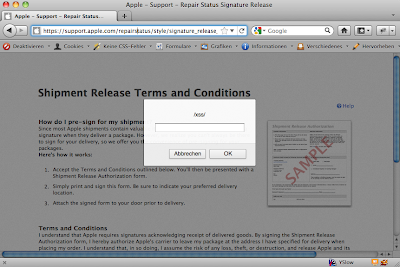
support.apple.com
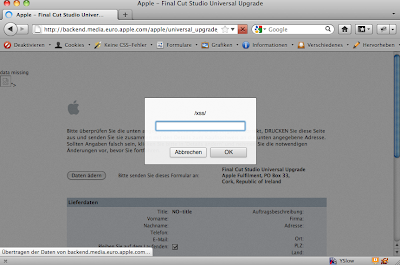
backenend.media.euro.apple.com
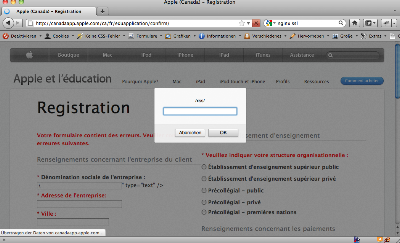
canadaedu.apple.com
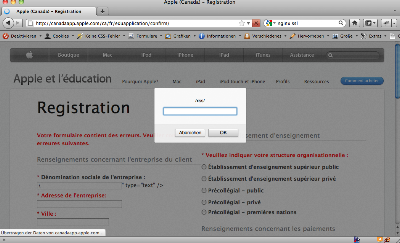
canadaedu.apple.com
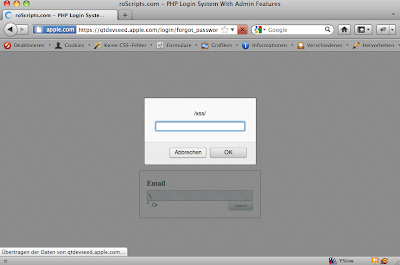
qtdevseed.apple.com